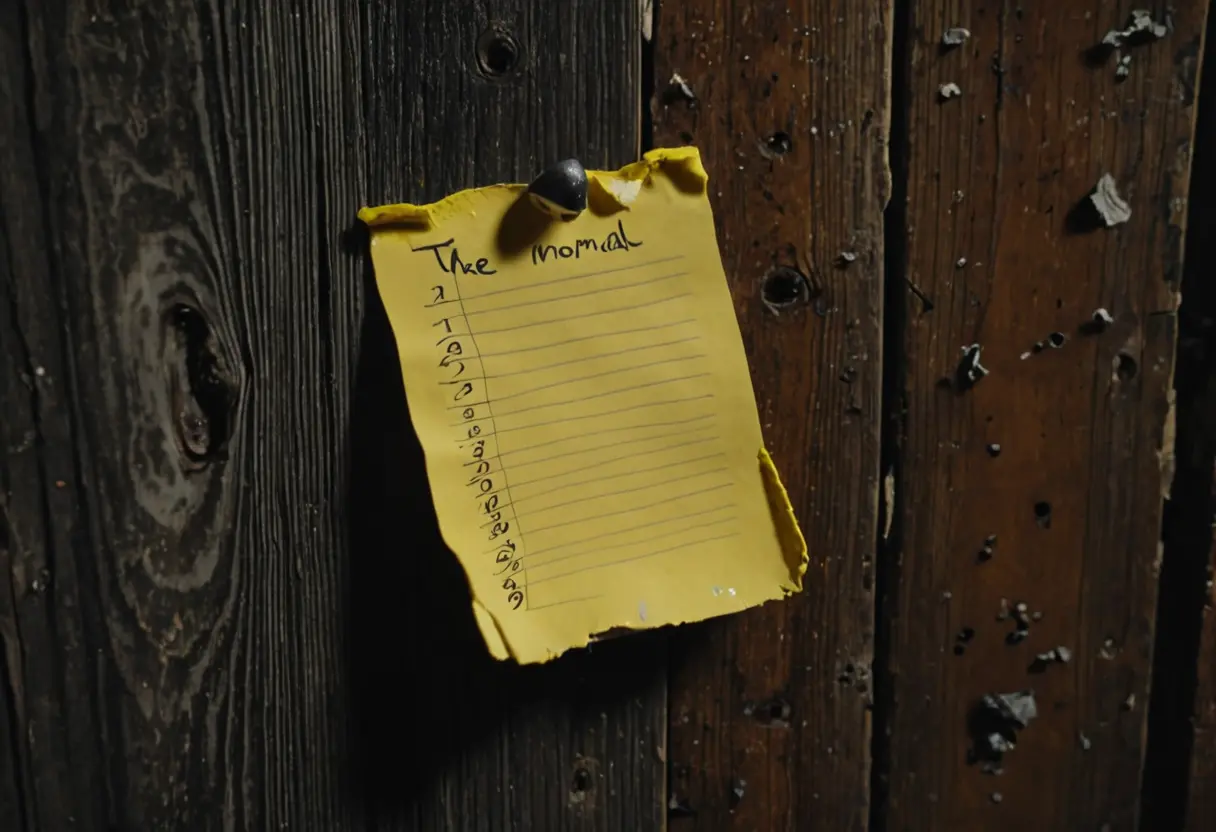
The Mystery List
1. Context Missing: Forced Mental Labor
The core of a “Mystery List” is the absolute lack of the “Why” or “How.” *The Hijacking of the Mundane :
・Milk
・Eggs
・Bread
・ Bleach (Extra Large) > ・ Hacksaw > ・ Her Shoes What starts as a mundane grocery list is high-jacked by a Secondary Objective . The transition from “Breakfast” to “Disposal” occurs in the whitespace between the lines. Your brain becomes the GPU that renders the gore.
2. Lists as Commands: The Metadata Breach
When a list reaches a certain point, it stops being “Information” and becomes a Command (Instruction) to the reader themselves. *Breaching the Fourth Wall : Imagine finding a “ToDo List” in your own phone that you didn’t write.
- Close the curtains.
- Lock the front door.
- Don’t look in the closet. The moment you read the 3rd item, the horror has successfully migrated from the screen into your Physical Reality . This is a “Targeted Meta-Attack” where you are no longer a reader; you are the Subject of the Protocol .
3. Search History: The “Thinking Log” of Madness
A modern variation of the list is the Search History Archive . Found on a second-hand laptop or a public terminal, these lists represent the “Trajectory of Obsession.” *The Path of Escalation : It starts with abstract searches like “Perfect Crime” or “How to remove blood,” then shifts into specific, predatory mapping: “Neighbor’s work schedule,” “Address (Your Home) entrance,” “Best way to hide a body in (Your Local Park).” *The Persistence of the Log : Unlike a ghost that disappears, a search history is a Persistent State of madness. It tells you that someone’s “Dark Mode” thinking is currently running in the background of your city.

Conclusion: The Danger of Patterns
A list is a tool for order. But when a drop of “Inhumanity” is added to the sequence, it becomes an Index of the Abyss .
If you find a random note in your pocket today with a list of names—and yours is the only one checked off—know that you are no longer part of a story. You are just an Entry in a Data Set that is about to be processed.
*The Night Shift Protocols : Managing the abnormal through rules. *Riddle Stories: The Logic of Understanding : When the inference is the trigger. *Internet Mysteries: The Search History Tabs : The digital footprint of the predator.